Moving content is the easy part.
In a GxP environment, regulatory requirements run through every decision — every transfer, every access control choice, every deviation from the plan. Most teams don't underestimate the technical complexity. They underestimate what GxP adds to it.
Delivered at multiple top-10 pharma companies.
Where GxP complexity lives in data migration
Data Mapping
Legacy-to-target translation must be solved before you move a single byte — for code, data, and structure.
Auditability
Can you prove things changed only when and how you said? Transparency is required from start to finish.
Access Control
Not a post-migration task. Unauthorized access to study data is a regulatory event.
Documentation
A plan before, a report after, and a deviation record. Every pharma defines their own requirements — does your migration process support them?

Content migration in a GxP environment takes more than technology
"The technical challenges are solvable. Derailments are almost always in planning, mapping, and governance — not execution."
Controlled. Not big bang.
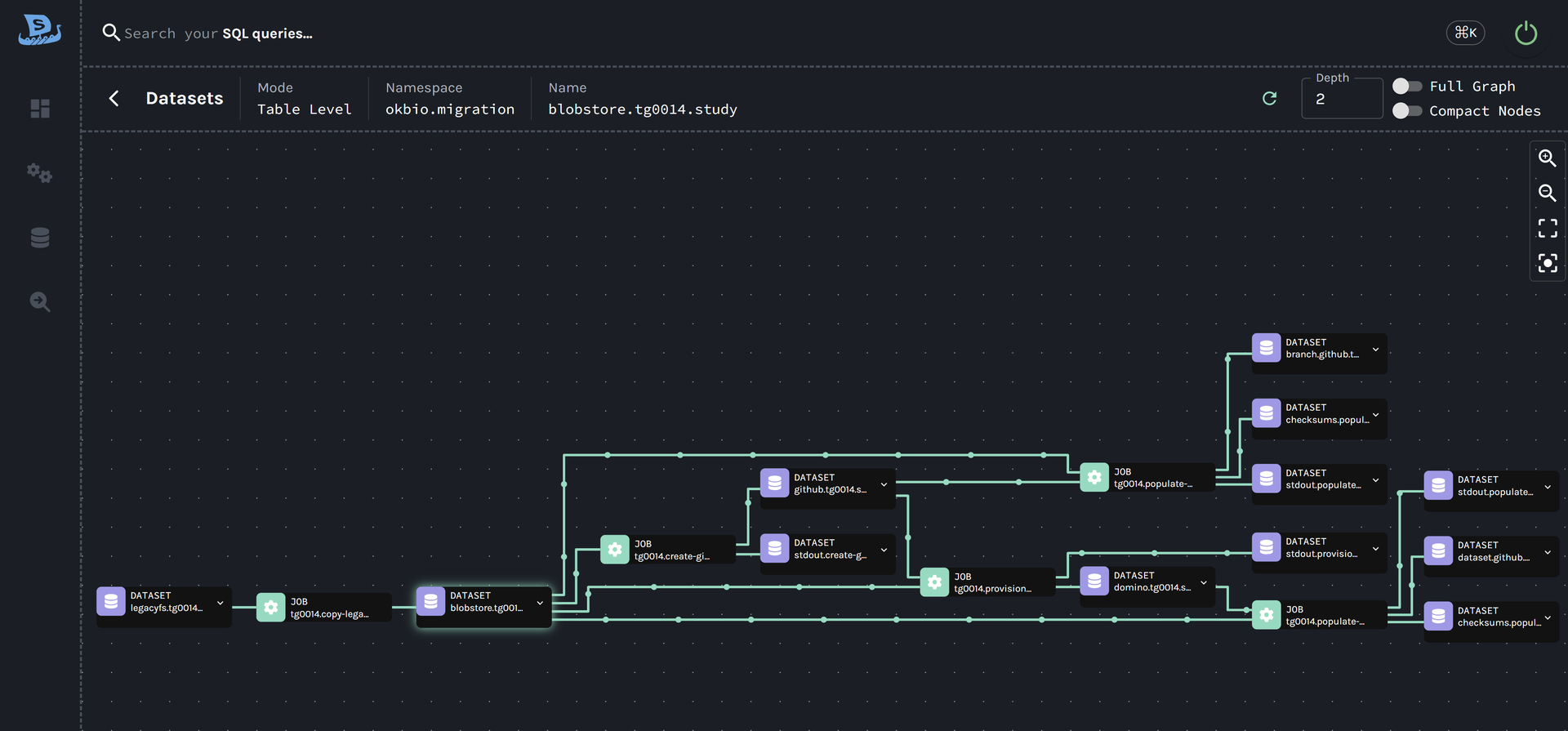
We break the migration into executable, governable units — study-level groupings with discrete ownership, independent state, and safe retry. Active studies don't get disrupted. Cutover happens in managed waves.
Migration Units
Study-level or equivalent groupings with clear ownership and status.
Per-Unit State
Each unit tracks its own state independently — safely retryable without affecting completed work.
Controlled Cutover
Managed transitions in waves, not a single high-risk switchover.
Bounded Scope
Clearly defined operational limits at every stage.
Most migrations weren't designed for GxP.
- Audit trail assembled after the fact from logs
- Access controls configured post-migration
- Big-bang cutover with high rollback risk
- Generic ETL tools adapted for regulated use
- Documentation produced manually at close
- Failed runs require restarting from scratch
- Lineage events emitted during execution — not reconstructed
- Access controls provisioned as code before cutover
- Controlled waves with per-unit state and safe retry
- KMT built ground-up for GxP regulated environments
- Documentation is a byproduct of execution
- Each unit retries independently — completed work is never re-run
Purpose-built tooling for regulated data migration into Domino.
The KSM Migration Toolkit (KMT) was built specifically for the challenges of migrating clinical data into modern platforms like Domino. This is not a generic ETL tool adapted for this use case. It was designed for it.
Infrastructure-as-code execution
Via Terraform — deterministic, repeatable, peer-reviewed before it touches target systems.
Native Domino connector
Provisions organizations, projects, volumes, access controls, and syncpoints as code.
Git-managed configuration
Every change is traceable, reviewable, and auditable.
Your QA team gets evidence, not assurances.
Documentation as a byproduct of execution — not assembled after the fact.
Timestamped Events
Every step emits a lineage event with a unique run ID — source to staging, staging to target.
Auto-attached Results
Validation results, checksums, and row counts automatically attached to the lineage record.
Built During Execution
A complete audit trail — not reconstructed from logs.
Deviation Records
When expected outcomes aren't met, it's captured and traceable.
Built for the teams who own the risk.
Regulatory complexity touches every stakeholder. KMT gives each team what they actually need.
Regulatory Affairs
Full audit trail, deviation records, and validation packages produced automatically — not assembled from spreadsheets after the fact.
Data Engineers
Infrastructure-as-code via Terraform. Git-managed configuration. Every migration unit is independently retryable without touching completed work.
IT & Security
Access controls provisioned before any data moves. Every permission is reviewable, peer-approved, and traceable to a Git commit.
Validation Teams
Checksums, row counts, and validation results auto-attached to every lineage record. Your IQ/OQ documentation is built during execution.
Study Operations
Active studies stay uninterrupted during migration waves. Cutover is managed, scoped, and reversible — not a single high-risk switchover.
Program Leadership
Clear migration unit status, controlled wave planning, and a defined engagement structure from scoping workshop through final cutover.
How an engagement unfolds.
-
Scoping Workshop
Data volumes, study types, source systems, regulatory constraints.
Output: a clear picture of what you're migrating, and when.
-
Mapping Exercise
Translate legacy model to target structure.
Output: validated mapping spec and migration unit definitions.
-
Pilot Migration
Execute first wave end-to-end. Produce first real validation package. Resolve edge cases.
-
Migration at Scale
Controlled waves with cutover management, lineage visibility, and audit-ready documentation throughout.
